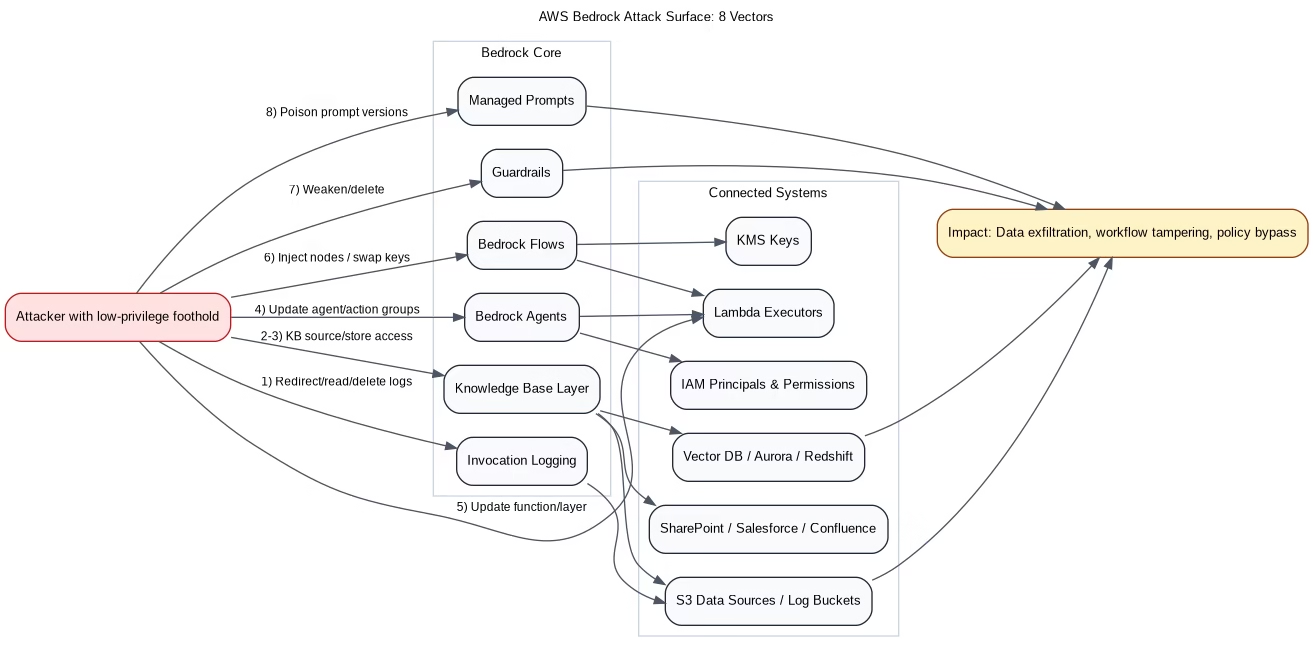
AWS Bedrock can become a high-impact attack pivot if permissions, integrations, and runtime controls are loose. The biggest risk is not “the model being hacked,” but attackers abusing adjacent components—logging, Knowledge Bases, agents, flows, guardrails, and managed prompts—to exfiltrate data or execute unauthorized actions. This guide breaks down eight practical attack paths and the exact hardening controls security teams should implement.
Why Bedrock Security Fails in Real Environments
Most Bedrock incidents start with over-permissioned IAM identities and weak change controls around AI plumbing. Once an attacker gets a foothold (compromised key, role abuse, CI/CD leak), they target integrations and orchestration layers where blast radius is highest.
- Logging sinks reveal prompts and sensitive context.
- Knowledge Bases expose enterprise data and connected SaaS credentials.
- Agents and flows can be modified to execute attacker logic.
- Guardrails and prompts can be silently weakened in-flight.
The 8 Bedrock Attack Paths (and How to Block Them)
1) Model Invocation Log Tampering or Redirection
Attack: Adversary reads sensitive prompts from log buckets, redirects logs to attacker-controlled storage, or deletes logs to erase traces.
Defenses: Immutable logging patterns, S3 Object Lock where possible, tight IAM on logging configuration APIs, and alerting for log-destination changes.
2) Knowledge Base Source Data Theft
Attack: Instead of querying through Bedrock, attacker directly accesses underlying S3/SaaS sources used by RAG pipelines.
Defenses: Segmented data access, per-source least privilege, scoped service roles, and explicit deny policies for non-approved principals.
3) Knowledge Store Credential Abuse (Vector DB / SQL Backends)
Attack: Credentials in configuration paths are abused to access vector indices or relational stores backing the knowledge system.
Defenses: Secret rotation, network segmentation, short-lived credentials, and policy checks on knowledge base configuration reads.
4) Direct Agent Hijack
Attack: Agent instructions or action groups are modified to leak internals or trigger unauthorized tool execution.
Defenses: Change approval workflows, signed agent config in GitOps, and drift detection for all agent prompt/tool definitions.
5) Indirect Agent Hijack via Lambda
Attack: Lambda function code/layers used by agents are replaced or poisoned, turning legitimate tool calls into exfiltration paths.
Defenses: Code signing, deployment role separation, immutable artifact promotion, and runtime egress controls.
6) Flow Injection and Control Bypass
Attack: Flow nodes are inserted to siphon data, conditions are altered to bypass business logic, or encryption keys are swapped.
Defenses: Protected flow templates, policy-based validation on publish, and mandatory approvals for condition/key changes.
7) Guardrail Degradation
Attack: Safety thresholds are reduced or guardrails removed, increasing prompt injection and data leakage risk.
Defenses: Guardrail baseline enforcement, automatic rollback on drift, and high-severity alerts for updates/deletes.
8) Managed Prompt Poisoning
Attack: Shared prompt templates are modified centrally, changing AI behavior across multiple apps without redeployments.
Defenses: Version pinning, signed prompt releases, approval gates, and prompt integrity scans in CI/CD.
Bedrock Hardening Blueprint (Practical)
- Identity: Deny-by-default + least privilege for Bedrock, Lambda, KMS, and storage APIs.
- Configuration: GitOps-managed agents/flows/prompts with approvals and audit trails.
- Secrets: Rotation, short TTL credentials, and strict secret-read boundaries.
- Detection: Alerts for high-risk mutating calls (update/delete on logs, guardrails, prompts, agents, flows).
- Containment: VPC endpoints, egress restrictions, and workload segmentation between AI and core data assets.
Recommended Internal Reads
- OpenClaw Architecture: How It Executes Tasks and What to Remember
- Amazon S3 Account Regional Namespace: Stop Fighting Over Bucket Names
- Redshift Materialized Views: How They Work, Why They’re Fast, and When to Use Them
FAQ: AWS Bedrock Security
Is Bedrock insecure by default?
Not inherently. Risk appears when IAM permissions are broad, changes are unmanaged, and integrations are not segmented.
What is the highest-priority control to implement first?
Lock down mutating API permissions (agent/flow/prompt/guardrail/log config updates) and alert on every high-risk change.
Can prompt poisoning affect multiple applications at once?
Yes. If multiple apps share centrally managed prompt templates, one poisoned version can propagate broadly.
How do I reduce blast radius in RAG pipelines?
Isolate data sources, use narrowly scoped service roles, rotate secrets, and restrict lateral movement from AI runtime components to core systems.
Editorial note: This post is an independent technical rewrite inspired by recent publicly discussed Bedrock attack research and focuses on practical defense implementation.